If we look into the recent surveys and reports on Temu, this question makes sense. While it’s obvious that this platform offers excellent deals, recent reports have raised questions about data privacy and product quality. As a result, some customers are pleased, while others have significant worries.
In this article, we will give you detailed insights on how Temu safety and legitimacy policies work and how you can manage to secure your data online while shopping at Temu. Let’s dig into what makes Temu so popular and how to shop safely in this rapidly growing online marketplace.
What is Temu?
Temu has quickly become a popular online marketplace since its launch in September 2022, operating under PDD Holdings Inc., the parent company of the Chinese e-commerce giant Pinduoduo. It serves as a one-stop shop where you can find a wide range of items, from fashion to home goods, all at surprisingly affordable prices.
The platform features products across various categories, including:
- Fashion and accessories
- Home and garden supplies
- Electronics and gadgets
- Beauty and health products
- Toys and entertainment items
- Pet supplies
Temu stands out because it follows a specific business model where products come directly from the manufacturers. This means Temu works closely with the companies that make the products instead of going through intermediaries. This approach helps reduce costs and allows customers to buy items at much cheaper rates.

Is Temu legit?
Yes, Temu is legit. Some people have a good online shopping experience with it, but some customers have concerns about data privacy, product quality, and poor customer support.
Is Temu safe to buy from
Temu has been facing several complaints online about privacy and data-related issues, but it is still working to make online shopping safe. The platform uses multiple security measures, including the most common encryption methods, ensuring your personal and payment information will be safe.
Temu has multiple layers of security for your transactions :
- 3D Secure authentication for credit card transactions
- PCI DSS Compliance for Credit Card Handling
- SSL encryption on all pages
- HTTPS security rules
Under the Purchase Protection Program, all purchases are risk-free. You get all your money back within 90 days if:
- Your items don’t match the description or photos
- Products arrive damaged
- Orders are lost in transit or delayed
Temu’s security system is similar to big websites like Amazon and eBay. The platform gathers a lot of user information, such as your name, email, address, phone number, and payment details, so you have to take an extra layer of protection by using a good VPN.
Important note: Temu keeps all user data safe by encrypting it and has easy refund processes to protect buyers. The platform shares some information with advertising, marketing, and analytics companies outside of itself.
Which payment method is used by Temu?
For safety in receiving payments, Temu has options for PayPal, credit cards, and digital wallets. It makes all your transactions safer because you don’t need to give the platform your card details.
Temu has security certifications and a safety center to assist the users. But privacy experts are concerned about how data is being gathered. Still, Temu uses standard security measures to protect financial information while making transactions.
Temu has strong security measures, but you have to take some basic online shopping safety tips.
Risks of using Temu
You should think over the risks of using Temu before rushing to grab those incredible deals because your online safety depends on it. Recent investigations have shown several problems that need your attention.
Data Privacy and Security Risks experts have labeled Temu’s app as “the most dangerous app in wide circulation.” The platform’s software has hidden functions that could collect extensive data from your device. It can access your device’s camera and microphone, monitor your emails and messages, track your location through GPS, log your Wi-Fi connectivity data, and access your contact lists.

Malware and surveillance concerns
The risks to your privacy are bigger than you might think. Grizzly Research, a market intelligence firm, warns that the app shows signs of “the most aggressive forms of malware/spyware.”
Users have filed many class action cases. They argue that the Temu app accesses “almost everything on a user’s phone” once downloaded.
Data breach and third-party access
Temu says that they do not “sell” your data directly. They share your information with marketing firms, consumer research companies, advertisers partners, and analytics firms.
This shopping application might also pose a threat to your data privacy. This application has numerous class-action lawsuits filed against it, where people claim that it could have access to almost all your phone contents. These contain simple information like your name and address, personal details like your IP address, and your browsing history.
Quality issues in products and services
The Better Business Bureau received over 1,748 customer complaints about Temu in just one year. Customers often say broken packages, unexpected charges, wrong orders, and unresponsive customer service.
The business model raises questions about the authenticity of the product and quality control of the platform. Also, 94% of imports enter the U.S. through De Minimis rules. This increases your chances of getting fake or low-quality products significantly.
Financial security factors
Temu has very critical security measures in place for their transactions. However, they collect a lot of information that could put your financial details at risk. A class action lawsuit from September 2023 says that Temu “grossly failed to comply with security standards and allowed its customers’ financial information to be compromised.”

Other issues related to Temu
Delivery delays
Customers who order from Temu tend to experience problems with late deliveries because their standard shipping takes 7 to 15 business days, which is more than most American shops. The BBB has several complaints about missing packages and odd charges, too.
Lack of transparency
Temu has some transparency issues that raise questions about its practices:
- The BBB gave the platform a C+ rating, which reflects a mix of complaints and unresolved issues regarding customer satisfaction and trust.
- No one knows how they comply with the Uyghur Forced Labor Act, a U.S. law designed to prevent forced labor in Xinjiang, China, from entering American markets. This raises concerns about the ethically sourced products of Temu.
- It uses tax loopholes to avoid U.S. commerce regulations. Due to this, not only does this company have an advantage over others, but its commitment to fair trade and ethical business practices becomes very questionable.
Fake promo codes
Be cautious of fake promotions on Temu. Scammers create fake social media posts that promise free items or big discounts using fake referral codes. These tricks exploit the referral rewards system on Temu and only help the scammers earn money.
Temu is indeed a real platform but with a relatively low BBB rating of 2.5 stars, which shows that its customers are worried about its business practices and customer service.
How to use Temu safely?
Shopping on Temu safely does involve a few security measures that ensure your personal and financial information is safe. Let’s go over what you should do for a safe shopping experience.
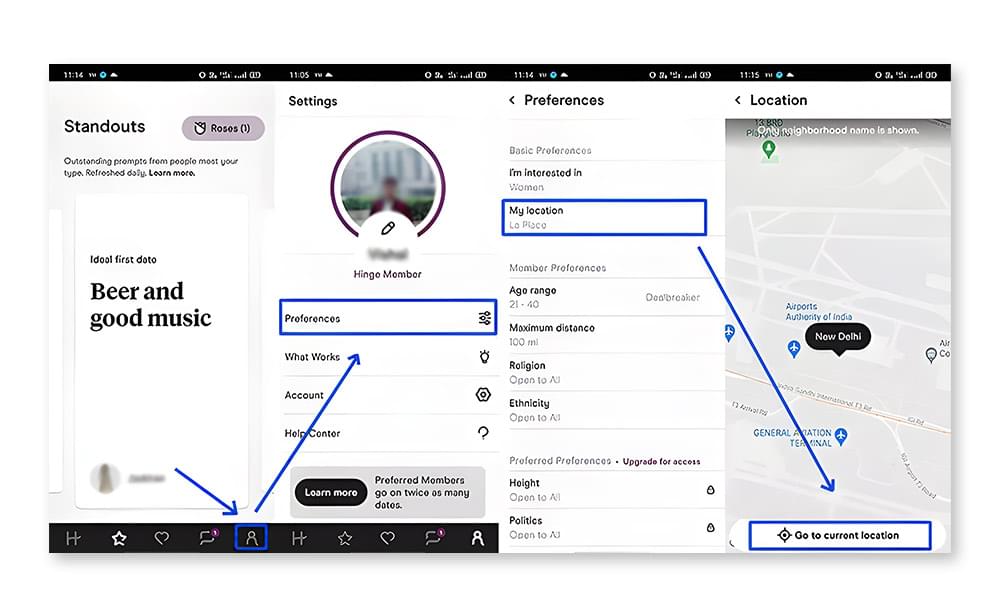
Use a VPN
A VPN is a vital part of shopping on Temu because it encrypts your internet connection and shields your online activities from potential threats. A reliable VPN service should give you:
- Military-grade encryption
- No-log policy
- Protection against data leaks
- Secure server connections
Using a VPN while shopping online is a great safety measure as it prevents scammers and ISPs from accessing or disclosing your activities. Additionally, a VPN can protect your online privacy by masking your IP address, making it harder for advertisers and websites to track your browsing history.
Be selective with your personal information
While using Temu, try to share only the minimum data and keep the personal information on Temu private. If you’re using an iPhone, try the “Hide My Email” feature that lets you generate a random email address when opening an account on Temu. This random email receives the messages in your iCloud email. You can quickly turn it off if you get too much spam.
If you do not have an iPhone, don’t worry. Most e-mail services enable you to create temporary email addresses for sites that you don’t entirely trust or to avoid filling your inbox.

Use secure browser
Search through a safe web browser with an encryption of HTTPs for Temu. This keeps your private information safe from possible dangers.
Avoid clicking on any suspicious links, spyware emails, or ads that pop up on your screens. Also, be careful to verify the website address before entering your personal information.
Check seller reviews
You should see the seller ratings and customer reviews of the product fully before buying. Always check for sellers that have a lot of good feedback, recent customer reviews, clear product descriptions, and successful deals.
Use a secure payment method.
Your bank account should never connect directly to Temu. Pick secure payment options like PayPal, Apple Pay, Google Pay, and credit cards with fraud protection.
Track your order status and utilize Temu’s Purchase Protection Program if necessary.
Avoid making large purchases.
Always start with a small purchase. Temu is really good at offering affordable products instead of expensive ones, so smaller purchases are the way to go while experimenting with this site.
Use antivirus
Good antivirus software protects you from malware and phishing attacks. Your security software needs updates frequently to protect against new online dangers.
Conclusion
When shopping on Temu, you should consider the risks and rewards. The site has good prices, but you need to pay attention to issues like data privacy, product quality, and cyber security.
You can secure your online shopping by using VPNs, selecting secure payment means, reducing personal information disclosure, or simply protecting data and funds through any purchases made on Temu.
No deal should ever have you at risk. Know that you are buying and start very small. Protecting one’s personal information should be very important. These safety features will help you shop very safely in Temu.
FAQs
Is Temu a scam?
Temu is not a scam; it is indeed an e-commerce platform owned by PDD Holdings Inc. But like any other online marketplace, some frauds also find their way into it. The Better Business Bureau issued Temu a C+ rating after handling 1,748 customer complaints for the year.
Why is Temu so cheap?
The low prices of Temu products are due to a few key factors. They ship products directly from Chinese manufacturers, which cuts out middleman costs. On top of that, they take advantage of the De Minimis Tax Exemption, so packages under $800 enter the US without specific duties or tax charges. It’s worth mentioning that these pricing strategies cost the company between $588 and $954 million each year.
Does Temu steal your information?
Temu does not really take the user data. However, security experts have cited some major complaints about data collection practices within the app. They found that it possesses hidden functions that are programmed for extensive data exfiltration.
It has already caused several class-action suits, and it has been labeled as a “data theft business selling products online” by Arkansas Attorney General Tim Griffin.
What data does Temu collect from you?
Temu collects quite a lot of your personal information:
- Your name, email, and phone number
- Home address and payment details
- Purchase history and browsing patterns
- Device data and location information
- Photos and videos (if permitted)
- Social media profile links
This data can be used by third-party advertising companies.
]]>